These days, with so much of our lives happening online, end-to-end encryption (E2EE) is one of the best ways to keep your private stuff private. Unlike basic encryption, E2EE makes sure only the person you’re talking to can read the data—not hackers, not snoops, and not even the company running the service. Here’s what E2EE is, why it matters, how it works behind the scenes, and what it looks like in real life (including some of the trade-offs). If you worry about surveillance, data leaks, or cyber attacks, knowing how E2EE works helps you make smarter choices about protecting your information.
End-to-End Encryption: Why It Matters
When it comes to digital privacy, end-to-end encryption (E2EE) is one of the strongest protections you can have. It goes beyond the kind of encryption you get with a standard HTTPS connection. With E2EE, your data stays locked down so that only the intended recipient can unlock it. Not even the service provider can read what you send.
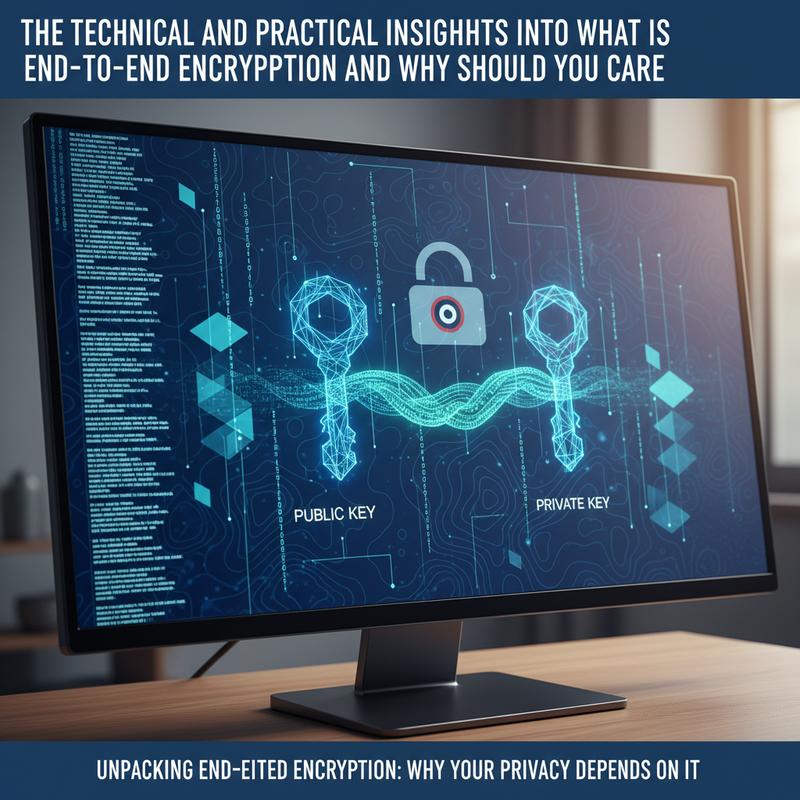
E2EE works by using a public key to encrypt data on the sender’s device, and a matching private key to decrypt it on the recipient’s device. Once the data is encrypted, it becomes unreadable as it moves through servers, because nobody in the middle has the private key. When it arrives, the recipient’s device uses the private key to turn it back into something readable.
Thing is, to really get why E2EE is so effective, it helps to understand the mechanics of E2EE. It usually combines asymmetric encryption (for swapping keys safely) with symmetric encryption like AES-256 (for encrypting the actual message or file). Many E2EE systems—like the Signal Protocol—also use forward secrecy, which creates new keys for each session. So even if one key ever leaks, it won’t expose your past or future messages.
The real-world impact of E2EE is huge. It makes mass surveillance harder, and it gives people more protection from unwanted monitoring. The 2013 Snowden leaks highlighted how government agencies could take advantage of communications that weren’t protected with E2EE. And today, protections like this still matter a lot, especially in places facing extra scrutiny under laws like the EU’s Digital Services Act.
On the flip side, E2EE also helps reduce the damage from data breaches, which sadly aren’t rare anymore. Big incidents like Equifax and Yahoo showed how exposed systems can be when strong encryption isn’t in place. With E2EE, even if someone steals the data, it’s still scrambled and basically worthless without the keys. That extra layer matters as attacks keep getting more advanced.
From a business and privacy angle, E2EE can also limit how much your information can be mined for advertising or other tracking. In a world where companies constantly collect user data, encrypting messages can help block unauthorized collection and keep conversations more personal. The Federal Trade Commission’s reports from 2024 point to unencrypted data as a major driver of the growing surveillance economy, which is another strong reason to take encryption seriously.
And E2EE matters when it comes to law enforcement access, too. It can protect personal messages from broad fishing expeditions and push back against encryption “backdoors,” which often create new security risks for everyone. Keeping encryption intact means you keep control of who can read your data.
Now, looking ahead, quantum computing could create new problems for today’s cryptography. But E2EE isn’t standing still—it’s starting to adopt post-quantum algorithms so it can stay secure even against future threats. Apps like Signal are known for staying on top of these changes and updating their approach as the tech moves forward.
So, end-to-end encryption isn’t just a nice-to-have. It’s one of the best tools we have for private communication in a world where threats keep changing. If you want more ways to tighten up your security, check out 5 cybersecurity habits every small business must adopt.
How End-to-End Encryption Works in Real Life
End-to-end encryption (E2EE) is a big part of modern privacy because it acts like a lockbox only the recipient can open. Even when the internet is full of risks, E2EE keeps messages hidden from everyone else—including the service provider. Depending on the setup, it can protect data while it’s stored, while it’s being sent, and sometimes even while it’s being handled.
To understand the technical mechanics of E2EE, you need to look at how asymmetric and symmetric encryption work together. Asymmetric cryptography uses two keys: a public key you can share and a private key you keep on your device. In practice, the sender uses the recipient’s public key to encrypt a temporary session key. Then symmetric encryption (like AES-256) uses that session key to encrypt the actual message. Only the recipient’s private key can unlock the session key—and that’s what keeps the message protected.
This setup also supports forward secrecy by creating fresh keys for each message or session. That way, if one key gets exposed, it doesn’t open the door to everything you’ve ever sent. In many systems, the provider only ever sees encrypted data and can’t decrypt it.
Still, E2EE isn’t magic. Even strong E2EE can’t always hide metadata, like who you talked to and when. And if someone compromises your device, or if key management is sloppy and allows man-in-the-middle attacks, encryption alone won’t save the day.
From a practical perspective, using E2EE cuts down the risks of interception and data theft, whether that comes from criminals or even a service provider acting in bad faith. And if a provider is legally forced to hand over data, E2EE can block access to the contents—because the provider doesn’t have the keys needed to read it.
That’s why E2EE has become a standard expectation for messaging. Apps like Signal and WhatsApp use an initial secure handshake when you first connect, then keep protecting ongoing chats with session keys. And with cloud storage, true E2EE means data is encrypted locally before it’s uploaded, so the servers become more like “dumb storage” that can’t read what they’re holding.
So, E2EE isn’t just a buzzword—it’s a major part of how people stay safer online. If you want more practical steps to improve security, you can also read 5 cybersecurity habits every small business must adopt. Once you understand what E2EE does (and what it doesn’t), it’s easier to pick tools that actually protect you.
What E2EE Does (and Why People Rely on It)
Sending messages online isn’t just about getting data from one place to another. You also need a way to stop other people from reading it along the way. End-to-End Encryption (E2EE) does exactly that by encrypting data on the sender’s device and only decrypting it on the recipient’s device. That means even the service provider can’t see what’s inside.
E2EE is built around public key cryptography. Each device has a key pair: a public key for encrypting and a private key for decrypting. The private key stays on the device, which is a big part of why this works. Then there are session keys, which speed things up for day-to-day messaging. These keys are often refreshed through forward secrecy—sometimes per message—so if a key ever gets compromised, older conversations are still protected.
For people and businesses, E2EE has a clear benefit: strong privacy protection from start to finish. Traditional encryption can expose messages at certain points, like when data passes through servers. E2EE avoids that by keeping the content locked the whole way. And if a provider gets breached, the stolen data is still unreadable.
E2EE also gives users fine-grained control over access to their own data. Since the keys stay with the user, the user decides who gets in. That matters in regulated industries like finance and healthcare, where data protection rules can be strict. And yes, destroying encryption keys can make data permanently inaccessible, which can support legal requirements like the “Right to be Forgotten.”
As E2EE becomes more common, it also fits nicely with a Zero-Trust security model, which is basically “never trust, always verify.” Instead of assuming anything inside a network is safe, Zero-Trust checks access at every step. E2EE supports that approach by keeping data encrypted in storage and in transit.
Looking forward, E2EE is also likely to grow alongside ideas like Confidential Computing, which aims to keep data encrypted even while it’s being processed. That could make it safer to run sensitive workloads in the cloud, including AI and analytics, without exposing raw data. And as quantum computing advances, E2EE will need to keep adapting to stay reliable.
At the end of the day, E2EE is one of the most practical tools we have for privacy online. As more messaging apps and cloud services adopt it, the core cryptography behind it will keep shaping what “secure communication” looks like.
Final thoughts
End-to-end encryption isn’t just a tech phrase—it’s a key part of staying safe online. Threats keep changing, so it helps to understand what E2EE does, why it matters, and where its limits are. If you know the basics, use good habits, and pick services that take encryption seriously, you’ll be in a much better spot to protect your personal data. And yes, choosing encrypted tools doesn’t just help you—it helps make the internet a little safer for everyone.
Want a simple next step? Turn on end-to-end encryption where you can, and stick with apps and services that keep the keys in your hands.
Learn more: https://itcarolina.com/about/
About us
At IT Carolina, we focus on keeping your online privacy and security strong without messing up your entertainment setup. Our technicians can tune your gaming and home entertainment systems and make sure they’re set up with the latest encryption options for better privacy. If you want things running fast and locked down, IT Carolina can help.